Security testing flash applications with AMF
Adobe Flash has become a popular platform for implementing rich internet applications (RIA). While the Flash Player itself has been plagued by numerous remote code execution vulnerabilities over the years, the security testing of Flash-based web applications introduces a different set of challenges altogether.
Unlike traditional web applications, Flash applications often communicate with backend services using binary protocols, making interception, inspection, and modification of traffic significantly more difficult.
This post provides an overview of Flash application internals, the ActionScript Message Format (AMF), and describes how we developed a custom AMF plugin for WebScarab can simplify the testing of Flash-based applications.
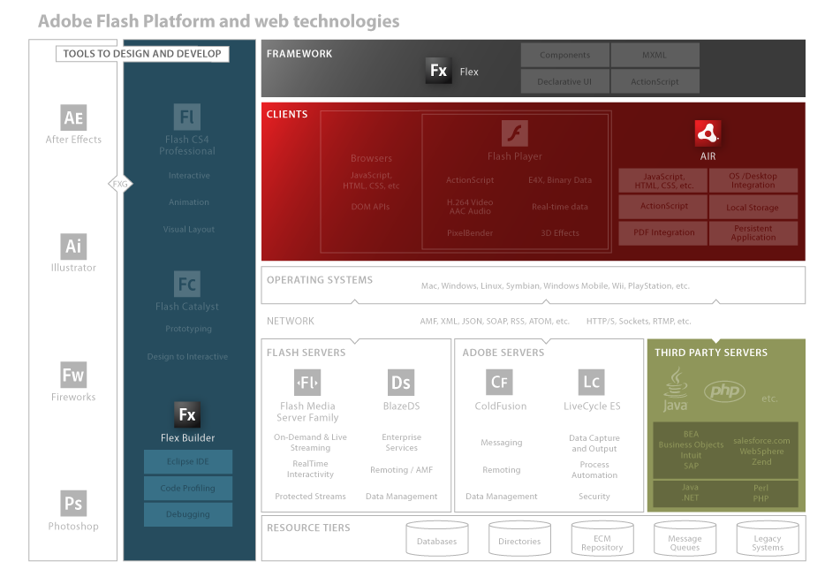
The Adobe Flash ecosystem
The Adobe Flash ecosystem consists of several components
- Flash: Originally used for animations, ads, and integrating video, it has evolved to support full-featured RIAs. It relies on ActionScript (versions 1, 2, & 3) for logic.
- Flash Player: The browser plugin that executes the compiled Flash content (SWF files).
- Flex: A framework specifically for developing RIAs. Developers design the GUI using MXML (an XML-based language) and handle programming with ActionScript.
- JavaScript Interaction: Flash applications frequently interact with the hosting web page via JavaScript.
ActionScript Message Format (AMF)
Most complex Flash applications need to talk to a server. They typically use AMF to exchange data between the client and the server-side component.
AMF is an asynchronous RPC (Remote Procedure Call) mechanism. Native Flash objects are serialized into binary data, sent to the server, and deserialized back into objects.
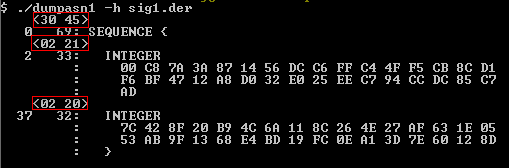
- Binary Format: Unlike clear-text XML or JSON, AMF is binary. It is similar to ASN.1, where data is encoded using Type-Length-Value (TLV) structures.
- Versions: There are two main versions you will encounter: AMF 0 (legacy) and AMF 3 (modern).
- Open Specs: Fortunately, Adobe has opened the specifications for these formats, making it easier for us to reverse-engineer the traffic.
The Remoting Envelope
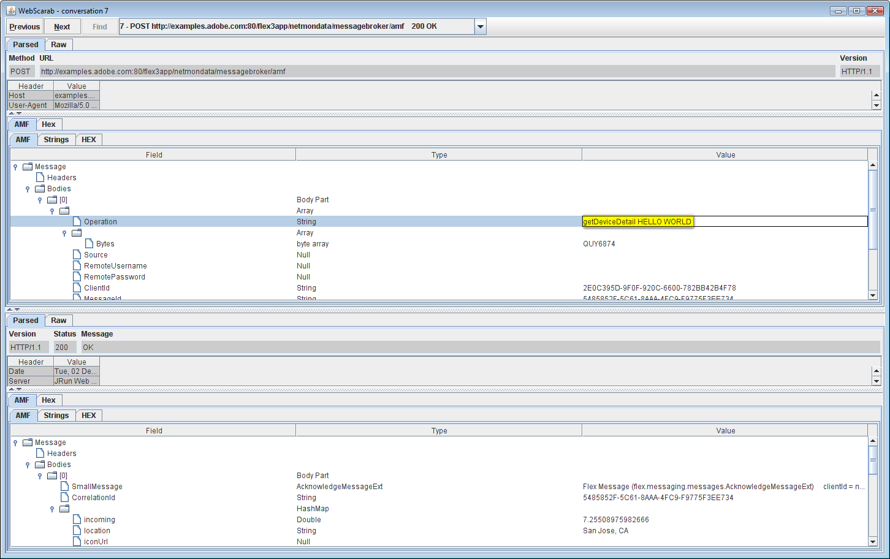
When you capture a Flash request, you aren’t just seeing raw data; you are seeing a “Remoting Envelope.” A typical packet consists of:
- Preamble: Indicates the version (0 or 3).
- Header(s): Contains metadata, names, and serialized AMF objects.
- Message(s): The core payload containing the Target URI, the Response URI, and the actual Data (serialized AMF object).
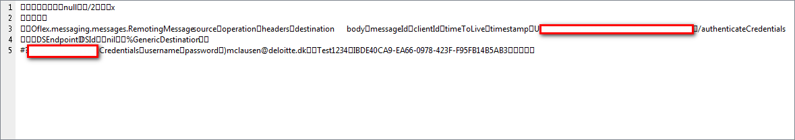
The Raw Request: Here is what the traffic looks like in a standard sniffer—mostly unintelligible binary noise:
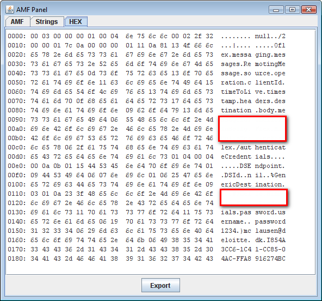
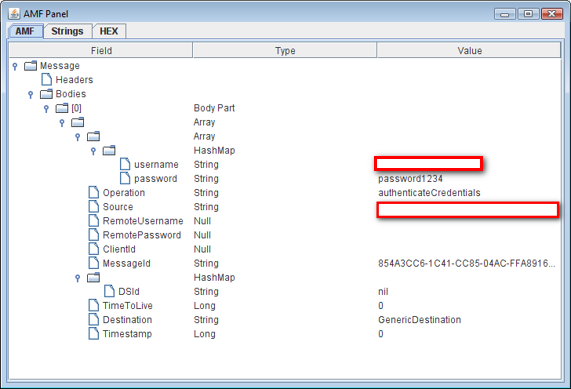
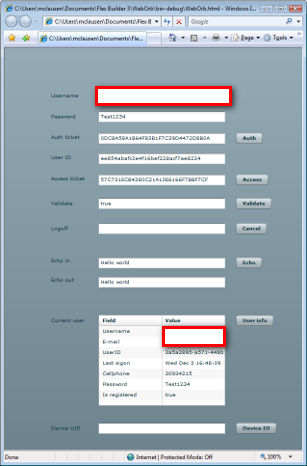
The Decoded Request: If we parse the binary structure properly, we can see the object hierarchy:
The Text Representation: The human-readable text values hidden inside:
Lack of Tooling
Testing these applications requires an interception proxy that can parse and modify this binary data. Unfortunately, the current landscape is lacking:
- WebScarab: Has basic support but is limited.
- Charles Proxy: Good visibility, but limited manipulation capabilities.
- ServiceCapture: Similar limitations.
- Burp Suite: Can capture the traffic, but modifying complex nested binary objects on the fly is extremely difficult without specific decoders.
The biggest issue is the lack of write support. Most tools allow you to read AMF, but they do not allow you to easily edit a parameter and re-serialize the packet correctly. Previously, the only workaround was to write a custom “wrapper” Flex application to act as a client, which is time-consuming and inefficient.
WebScarab AMF extension
To solve this, we have developed a custom extension for the WebScarab framework. WebScarab supports a plugin infrastructure, allowing us to override the default behavior.
Our new plugin offers significant improvements over the standard AMF support:
- Full Replacement: It completely replaces the existing plugin (which only read AMF 0).
- Version Support: It fully supports both AMF 0 and the newer AMF 3.
- Read & Write: Crucially, it creates a tree-view of the AMF messages that allows you to edit values. The plugin handles the complex re-serialization automatically before sending the request to the server.
References
- Testing Flash Applications (Stefano Di Paola / OWASP): http://www.wisec.it/en/Docs/flash_App_testing_Owasp07.pdf
- Adobe Flash Player 9 Security: http://www.adobe.com/devnet/flashplayer/articles/flash_player_9_security.pdf
- AMF 0 Specification: http://download.macromedia.com/pub/labs/amf/amf0_spec_121207.pdf
- AMF 3 Specification: http://download.macromedia.com/pub/labs/amf/amf3_spec_121207.pdf
- OWASP / WebScarab: http://www.owasp.org
- Open Source Flash: http://osflash.org